

Identity Threat Detection and Response (ITDR) Software
What is Identity Threat Detection and Response Software?
Identity Threat Detection and Response (ITDR) is a strategic solution in protecting user identities and systems from cyber threats. ITDR systems monitor user behaviors to detect strange login patterns or unauthorized access attempts, to quickly pinpoint and resolve possible security threats. When a threat is detected, ITDR solutions facilitate immediate actions, like isolating compromised accounts or requiring extra authentication measures, to mitigate risks and protect sensitive information.
Common Features
- Discover Machine Identities
- Discover Federated Identities
- Continuous Discovery
- ZSP support
- Authentication support
- Suspicious activity
- Time to value
- Forensics
- Policy Creation and Right Sizing
- Refactoring
- TTP detection
- Discover Human Identities
Our Methodology
Composite Score
Vendors are ranked by the composite score, which is comprised of feature, capability, relationship, and overall satisfaction scores while factoring in the volume and recency of reviews.
CX Score
The CX score is comprised of the emotional footprint metrics, balanced by metrics related to the overall value of the software, while factoring in the volume and recency of reviews.
Data Quadrant
SoftwareReviews collects user insights that help organizations more effectively choose software that meets their needs, measure business value, and improve selection.
Rankings, results, and positioning on SoftwareReviews reports are based entirely on end-user feedback solicited from a proprietary online survey engine.
Leaders
Products that resonate strongest in the market, balancing features with a great user experience.
Product Innovators
Products that emphasize product features, gaining strong recommendations from their customers.
Service Stars
Products that emphasize a good user experience and build strong relationships with customers.
Challengers
Products that are strong performers in some areas and trail in others. Often up-and-coming vendors.

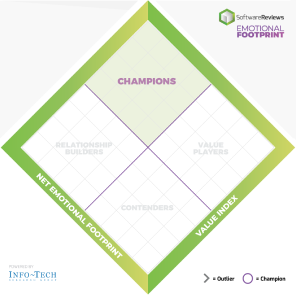
Emotional Footprint
SoftwareReviews collects user insights that help organizations more effectively choose software that meets their needs, measure business value, and improve selection.
Rankings, results, and positioning on SoftwareReviews reports are based entirely on end-user feedback solicited by a proprietary online survey engine.
Champions
Products that resonate highly with users at an emotional level. Users have specific emotional views towards these products like love, trust, and effectiveness.
Relationship Builders
Products that are bulletproof and focus on fulfilling core needs with steady support, not the latest feature.
Value Players
Products that succeed on cost and service effectiveness with users.
Contenders
Products seen as good in some areas and trailing in others. Users look to these for innovation at the edge but aren't fully committed.
Write a Review to receive up to a $10 Gift Card*
*After you complete our short 5-6 minute survey, we will happily provide you with your choice of reward up to $10 based on available options for your region.
Write a Review